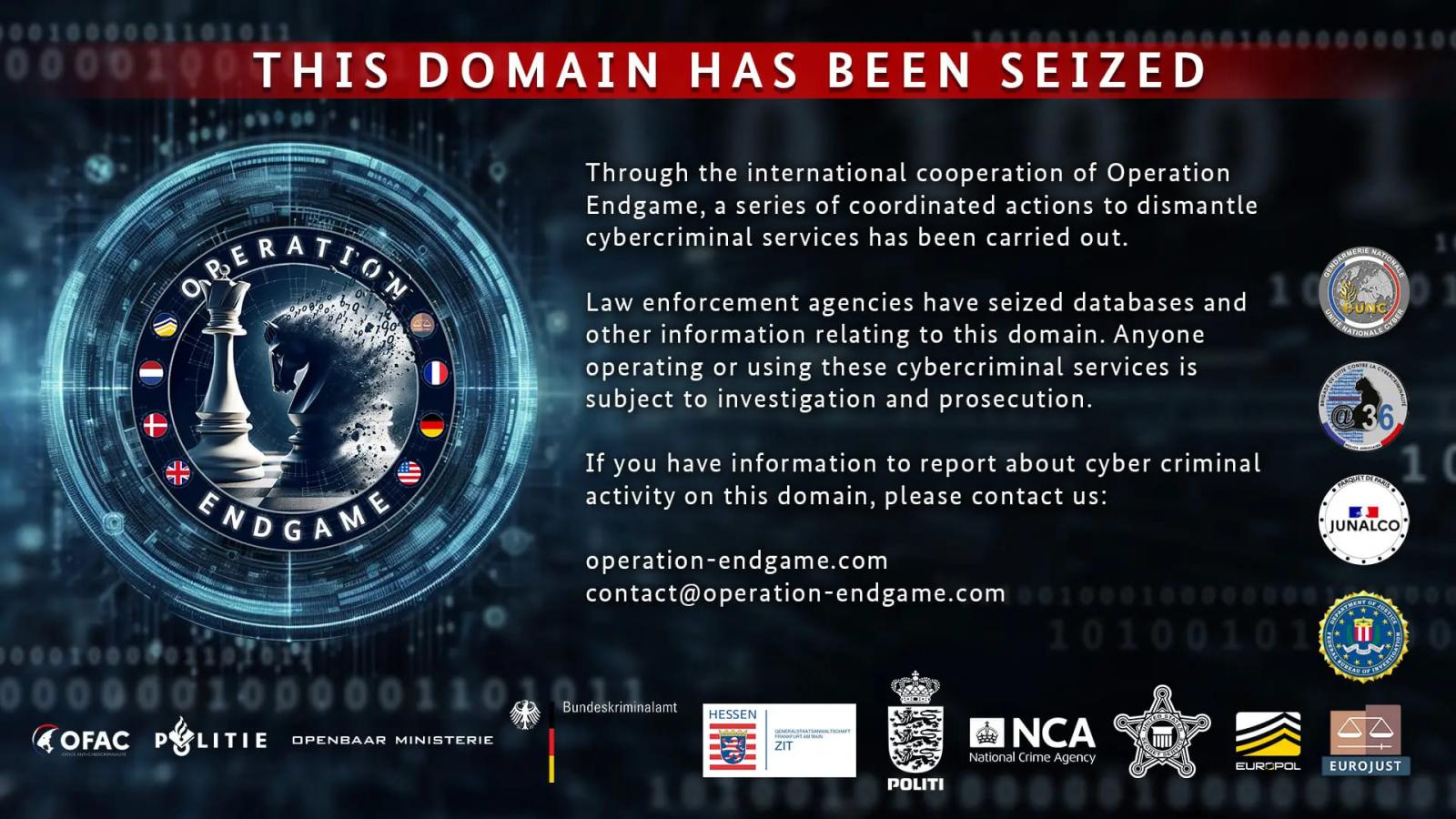
An international law enforcement operation codenamed ‘Operation Endgame’ has seized over 100 servers worldwide used by multiple major malware loader operations, including IcedID, Pikabot, Trickbot, Bumblebee, Smokeloader, and SystemBC.
The action, which occurred between May 27 and 29, 2024, involved 16 location searches across Europe and led to the arrest of four individuals, one in Armenia and three in Ukraine.
Additionally, the police have identified eight fugitives linked to the malware operations, who will be added to Europol’s ‘Most Wanted’ list later today.
The seized infrastructure was spread across Europe and North America, hosting over 2,000 domains that facilitated illicit services, all under the control of the authorities now.
Operation Endgame involved police forces from Germany, the United States, the United Kingdom, France, Denmark, and the Netherlands.
The operation was supported by intelligence provided by experts from Bitdefender, Cryptolaemus, Sekoia, Shadowserver, Team Cymru, Prodaft, Proofpoint, NFIR, Computest, Northwave, Fox-IT, HaveIBeenPwned, Spamhaus, and DIVD.
Millions of computers infected
Malware droppers are specialized tools designed to establish initial access to devices. The cybercriminals behind them typically send malicious emails to deliver the malware or hide payloads on trojanized installers promoted through malvertising or torrents.
Many of these droppers started as banking trojans and later evolved to focus on initial access, while also simplifying their operation and stripping out malicious features to reduce the likelihood of detection.
They employ evasive tactics such as heavy code obfuscation and legitimate process impersonation, often residing in memory.
Once the infection is established, they introduce more dangerous payloads to the compromised system, such as information stealers and ransomware.
Europol said that one of the main suspects involved in one of the targeted malware operations made over 69 million Euros ($74.5M) by renting out their infrastructure for ransomware deployment.
“It has been discovered through the investigations so far that one of the main suspects has earned at least EUR 69 million in cryptocurrency by renting out criminal infrastructure sites to deploy ransomware,” reads Europol’s announcement.
“The suspect’s transactions are constantly being monitored and legal permission to seize these assets upon future actions has already been obtained.”
More information about the suspects and the law enforcement operation is scheduled to be published on this dedicated portal later today.