All products are independently selected by our experts. To help us provide free impartial advice, we will earn an affiliate commission if you buy something. Click here to learn more
One of the largest ever databases of leaked passwordshas surfaced online, security researchers warned. The vast haul of stolen login credentials — with some 9,948,575,739 unique passwords stored in plain text — was posted on a forum popular with hackers at the end of last week.
Dubbed RockYou2024.txt, the file is bulging with stolen passwords that could unleash “a cascade of data breaches, financial frauds, and identity thefts,” according to the experts at CyberNews, who first uncovered the database shared by a forum user known only under the pseudonym ObamaCare.
It appears the database is a mixture of old and new data breaches.
“In its essence, the RockYou2024 leak is a compilation of real-world passwords used by individuals all over the world. Revealing that many passwords for threat actors substantially heightens the risk of credential stuffing attacks,” researchers said.
Credential stuffing is a popular form of attack that sees hackers use stolen login details from one website to attempt to log in to another. If you re-use the same username and password for multiple services, websites, and apps, then you’ll be susceptible to this type of cyber-attack.
A recent wave of attacks on Santander, Ticketmaster, and QuoteWizard are widely believed to be the direct result of credential stuffing attacks from victims’ of popular cloud service provider, Snowflake.
And now the team at CyberNews believe the same could happen with the latest database, cautioning: “Threat actors could exploit the RockYou2024 password compilation to conduct brute-force attacks and gain unauthorized access to various online accounts used by individuals who employ passwords included in the dataset.”
The database of stolen passwords was shared on a popular forum for hackers by someone with the username ObamaCare. Experts have verified that the text file does contain millions of passwords, building on the dataset initially released on the same forum three years ago
CYBERNEWS PRESS OFFICE
RockYou2024.txt builds on an earlier leak, RockYou2021.txt, shared by hackers online three years ago.
At the time, that text file packed with stolen usernames, email addresses, and matching passwords, was the largest stolen dataset of all-time — a record that’s since been broken by a leak researchers refer to as the “mother of all breaches”. Since the launch of RockYou2021.txt, some 1.5 billion passwords have been added to the database, putting millions more people at-risk of attack.
There’s no easy fix for anyone whose passwords are included in the RockYou2024.txt database.
However, the CyberNews team has shared some advice for those who want to protect themselves from credential stuffing or other types of attacks following the breach:
- Immediately reset passwords for all accounts that rely on a password included in the database
- Create a unique alpha-numeric password for each online account
- Enable multi-factor authentication, like a one-time code sent to your phone number, to protect accounts
- Use a password manager to store and manage complex passwords
- Use tools like haveibeenpwned.com/ to check whether your details have been breached
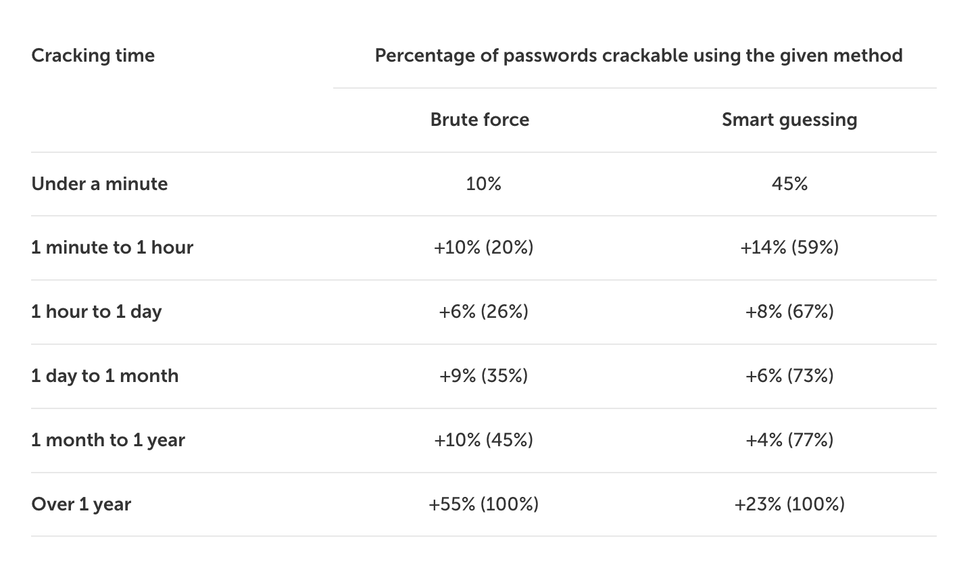
The dizzying database of leaked passwords comes just a few days after new research from Kaspersky has demonstrated that millions of popular passwords can be cracked in less than a minute, thanks to the improvements in computer hardware and smarter AI-equipped algorithms to break into online accounts.
Hackers attempted to break into passwords 32 million times last year alone, according to data from Kaspersky. That figure is likely to increase as it becomes easier and easier to brute-force passwords with the latest algorithm and hardware.
Kaspersky researchers used a combination of the latest algorithms and an Nvidia RTX 4090 GPU worth £1,549 to attempt to crack the database of 193 million passwords unearthed on the Dark Web. All of the passwords stored were hashed and salted — meaning researchers still needed to correctly guess them to break in.
If your password has 8 characters or fewer, it could be cracked in just 17 seconds, researchers found. Most of these passwords were either all lowercase or uppercase English letters with a few numerical digits — showing the importance of using special characters, like symbols, to make your password harder to crack.
In total, 45% of all passwords analysed from the database — 87 million — could be guessed within a minute.
The majority of the passwords examined by researchers contained at least one word from the dictionary, which significantly reduces the strength of a password and makes it more susceptible to brute force-style attacks.
As the researchers cracked millions of passwords, some patterns started to emerge. If you want to create a strong, unique password to shield your account, avoid some of these popular patterns —
Popular Words
- forever
- love
- hacker
- gamer
Common Names
- daniel
- kevin
- ahmed
- nguyen
- kumar
Standard Passwords
- password
- qwerty12345
- admin
- 12345
- team
Kaspersky analysed millions of hashed-and-salted passwords shared by hackers on the Dark Web to work out how long it would take to break into accounts
KASPERSKY
Kaspersky used a brute-force algorithm to achieve these results, a technique that’s very popular with hackers. This tries all possible password combinations by running through a list of words from the dictionary, as well as diverse character types, numbers, and more.
Researchers attempted to improve on the initial results by programming the algorithm to consider popular character combinations, common names, and sequences.
Hackers have also developed smart algorithms that make attempts with character replacements, like swapping an “a” for “@” or an “e” with “3” — so don’t do that when creating a password, it won’t make your account safer.
With the most efficient brute-force algorithm, researchers were able to break 59% of the 193 million passwords within an hour, and almost three-quarters of all passwords (73%) within a month.
Just 23% of passwords from the Dark Web database would take longer than a year to break.
Discussing their findings, the security experts from Kaspersky noted: “Unconsciously, human beings create ‘human’ passwords — containing the words from the dictionary in their native languages, featuring names, numbers, etc, things that are easy for our busy brains to recall easily.
“Even seemingly strong combinations are rarely completely random, so they can be guessed by algorithms. Given that, the most dependable solution is to generate a completely random password using modern and reliable password managers.”
Passkeys are an increasingly common solution to shield your accounts without relying on a lengthy alpha-numeric password that’s impossible to remember. This clever solution uses the security feature built into your smartphone — like Face ID facial recognition on iPhone, fingerprint scanners on Samsung Galaxy, and more — to verify your identity when you log in to a website or app.
Support for these password replacements is slowly being adopted by the biggest online services and applications, with Elon Musk enabling support on X for iPhone owners earlier this year, with WhatsApp also adopting passkeys to avoid its users relying on guessable passwords.
Password managers are another popular solution.
These standalone apps generate unique passwords with no discernable pattern at all — and a healthy mixture of lower- and uppercase characters, symbols, numerical digits, and much more. It would be impossible to memorise these long, unique jumbles of characters for every login, so password managers encrypt and save all of them for you — filling in the fields within apps and websites for you.
You’ll only need to remember a single password: the one that unlocks your password manager.
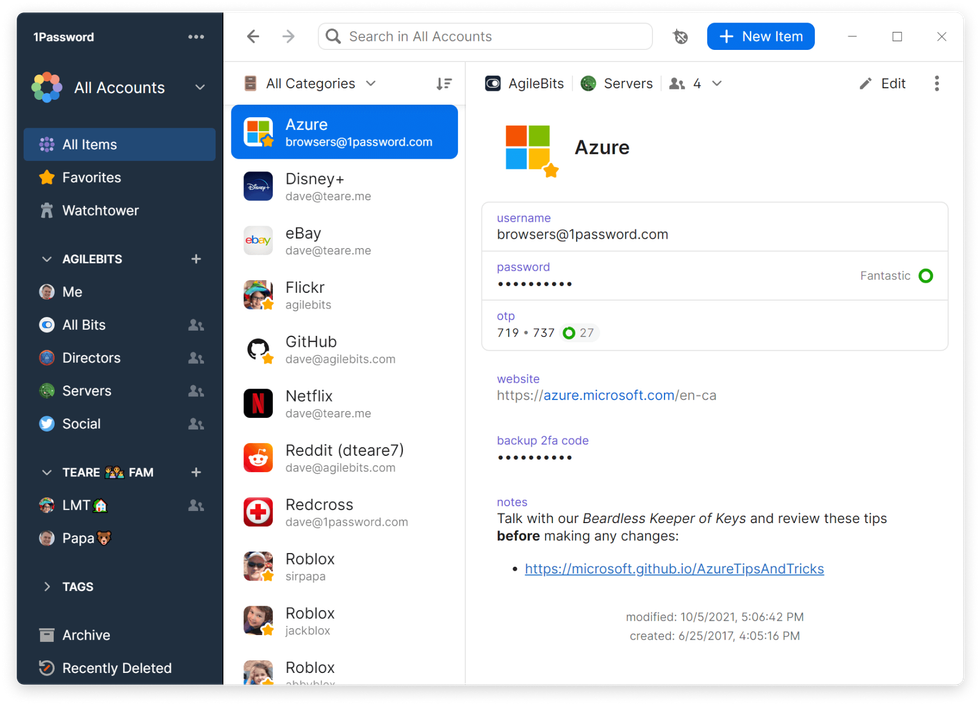
Password managers, like 1Password (pictured), can manage lengthy, unique alpha-numeric passwords for every online account and monitor the Dark Web for breaches and hacks
1PASSWORD PRESS OFFICE
Many of these applications also rely on biometrics, like fingerprints and facial scans, to lock down everything.
Apple includes a password manager — known as iCloud Keychain — as part of the mobile operating system that ships on every iPhone, iPad, and Mac, while Californian rival Google has baked in a similar system into Chrome. However, the iPhone manufacturer has big plans to overhaul this system with a true competitor to the likes of 1Password, NordPass, and LastPass in the coming months as part of its next free upgrade.
LATEST DEVELOPMENTS
In the last few months, we’ve seen security researchers unearth the so-called “mother of all breaches”, with billions of stolen usernames and passwords for popular sites like LinkedIn, X (formerly Twitter), Telegram, and Dropbox. Not only that, but hackers used credential stuffing to break into half a million Roku accounts and spend money using saved payment details.
Whatever you do, make sure you’re not using a password on this list published by Nord.